TL;DR: Commendable effort but it solves nothing.
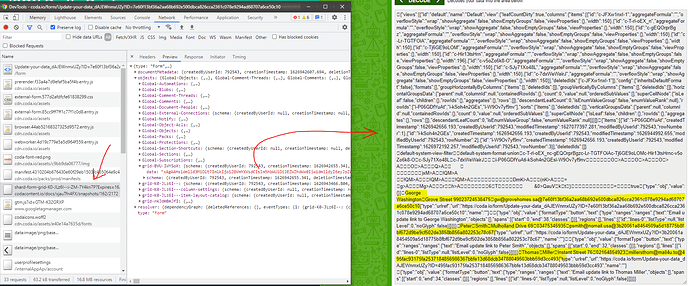
The “Update your data” form is insecure because you had to enable “Include lookup data” for the formulas to work, and that included the whole table of Personal Data (and also of the Updated Personal Data) in the shard that gets sent to the client where any attacker can crack it easily:
So, the only way to publish the form securely is to not include any existing data, no formulas or whatnot — only the fields to fill out.
At that point, SHA256 seems an unnecessary complication. If you wanted a pseudorandom row ID that would be hard to guess, you could use the Split(thisRow + "", "/").Last() idiom to get row UID — it is statistically enough. If you additionally wanted to prevent accidental form resubmissions, you could additionally include a version/timestamp parameter to catch those and not apply.